In its follow-up report published on Nov. 12, American-Israeli cybersecurity firm Check Point has tracked down the origin of Bitcoin ransomware that has successfully attacked numerous companies in Israel over the past few weeks.
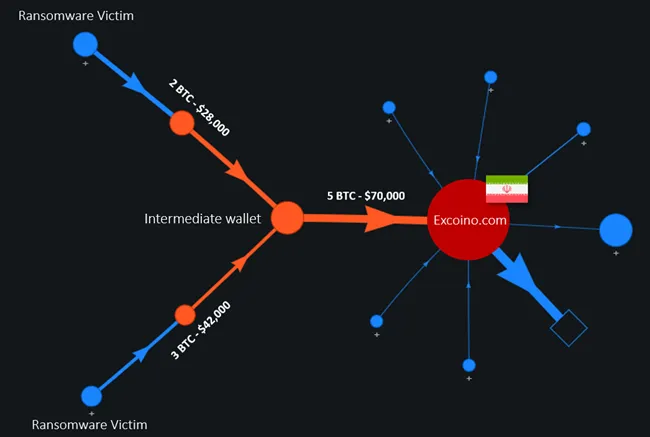
In partnership with blockchain forensics firm WhiteStream, Check Point researchers have linked a series of ransoms to Iranian cryptocurrency exchange Excoino after scrutinizing wallet addresses left in ransomware notes.
No trace of other ransomware strains
In late October, Israeli networks became the target of a sophisticated ransomware campaign dubbed "Pay2Key."
The attacks—which were not related to any previously known malware strains—were first covered in Check Point's security alert dated Nov. 6.
The ransomware is capable of encrypting the victim's computer within one hour. The bad actors have created an Onion website to leak the corporate data of non-paying companies:
So far, the non-paying victims of this double extortion attack are three Israeli companies, and by the time this report is published there might be more of them. The leaked data of each victim company was uploaded to a dedicated folder on the website, accompanied with a tailored message from the attackers.
Advertisement
Interestingly enough, whoever was behind the attack used an EOS logo on Keybase, but they most likely chose a random photo from Google Images.
Six-figure ransoms
The Check Point findings are not particularly surprising given the geopolitical tensions between the two countries. In 2020, the Iranian cyber force has carried out several attacks on the Israeli power grid.
The Pay2Key operators require their victims to pay relatively modest ransoms that range from 7 to 9 BTC ($112,000 to $114,000 at press time). So far, at least four companies have decided to comply with the hackers’ demands after their deposits were traced by blockchain sleuths.
As reported by U.Today, DarkSide hackers forced one corporation to pay over $1 mln before sending some of their proceeds to charities in a Robin Hood-like move.



 Dan Burgin
Dan Burgin