Finnish cybersecurity firm F-Secure has discovered a phishing attack against an unnamed cryptocurrency business that was evidently carried out by North Korean state-sponsored Lazarus Group.
Spreading malware via a fake LinkedIn job offer
The hackers targeted a sysadmin of the cryptocurrency organization by sending a fake job offer via the employment-oriented social media platform LinkedIn.
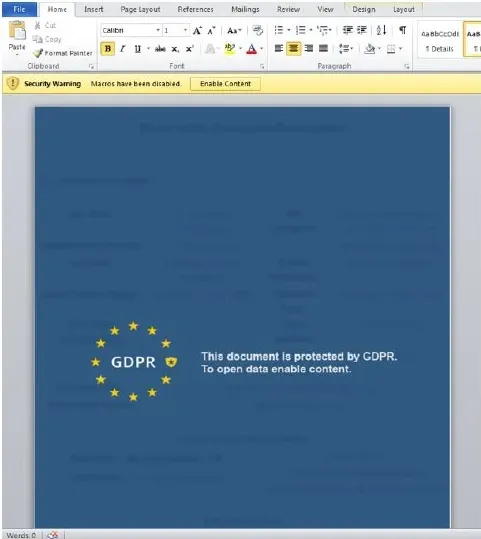
The private message sent to the victim contained a malware-infected Microsoft Word document.
Under the pretext of complying with the EU's regulatory requirements, it requires the user to enable macros in order to view the content.
Having been granted permission, the malicious macro code was then able to send information to the centralized computer controlled by Lazarus Group.
F-Secure says that Lazarus Group disabled the anti-virus software on the victim's computer in order to go unnoticed:
Lazarus Group invested significant effort to evade the target organization's defences during the attack, such as by disabling anti-virus software on the compromised hosts, and removing evidence of their malicious implants.
North Korea is on the hunt for crypto
The phishing attack is part of a widespread campaign that is specifically targeting cryptocurrency-oriented businesses in at least 14 countries, which include the U.S, the U.K and Japan.
North Korea has a notorious reputation for hacking cryptocurrency exchanges. According to a March 2019 report compiled by the U.N. Security Council, it amassed $670 mln worth of stolen fiat and crypto to fund its nuclear program.
The hermit kingdom, however, vehemently denied these allegations and called them "rumors" despite overwhelming evidence:
Such a fabrication by the hostile forces is nothing but a sort of a nasty game aimed at tarnishing the image of our Republic and finding justification for sanctions and pressure campaign against the DPRK.
Lazarus Group is also behind the WannaCry ransomware attack that infected more than 300,000 computers in 2017, demanding Bitcoin payments.



 Dan Burgin
Dan Burgin