Four scholars from the School of Engineering and Applied Sciences at Harvard University, Michael Neuder, Daniel J. Moroz, Rithvik Rao and David C. Parkesk, described two strategies for attacking Ethereum 2.0 Phase 0, or Beacon Chain.
Malicious reorganizations, finality delays: Two attack designs for extremely powerful staker
Starting from the introduction of Ethereum 2.0 architecture, the researchers revealed several scenarios for possible attacks against the network. In their paper, Harvard engineers recalled studies of sending conflicting attestations, exploring network latency issues and so on.
Meanwhile, they note, an attacker can maliciously attest the wrong block, initiating so-called "private forks." Attesting one "wrong" block would cause only minor reorganization, but this scenario could be extended to the performance of devastating attacks.
The second scenario includes a delay in block finality: the hypothetical attacker could delay finality, preventing the correct block from being attested. In this scenario, the attacker needs to be recognized as a proposer of a block boundary and, therefore, the first block of the next epoch.
Therefore, he/she needs to delay finality, i.e., to ensure that two consecutive blocks will not be attested in a fair manner. This scenario is less probable and far more expensive.
How much does it cost?
To start with, we need to evaluate the cost of a 30% stake in Ethereum 2.0. According to the dashboard by Etherscan explorer, now more than $6.6 billion in Ethers are transferred to the Ethereum 2.0 deposit contract.
Thus, to obtain the control of 30 percent of a stake, the attacker should spend almost $2 billion.
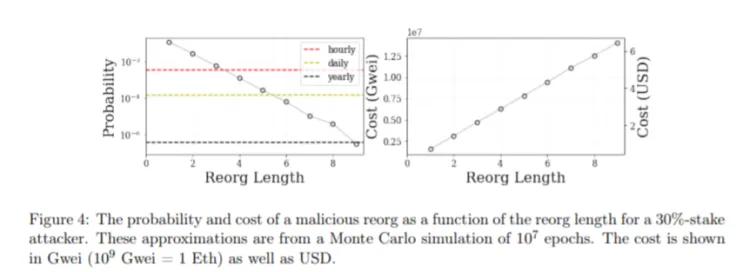
Once this milestone is accomplished, in the first scenario, he/she should spent (n-1) USD for each n-long reorganization, where n refers to the quantity of maliciously attested blocks.
The second scenario sould take between 500 and 1,200 U.S. dollars for every series of finality delays. Both designs imply 0.09 probability for a successful attack.

 Dan Burgin
Dan Burgin U.Today Editorial Team
U.Today Editorial Team