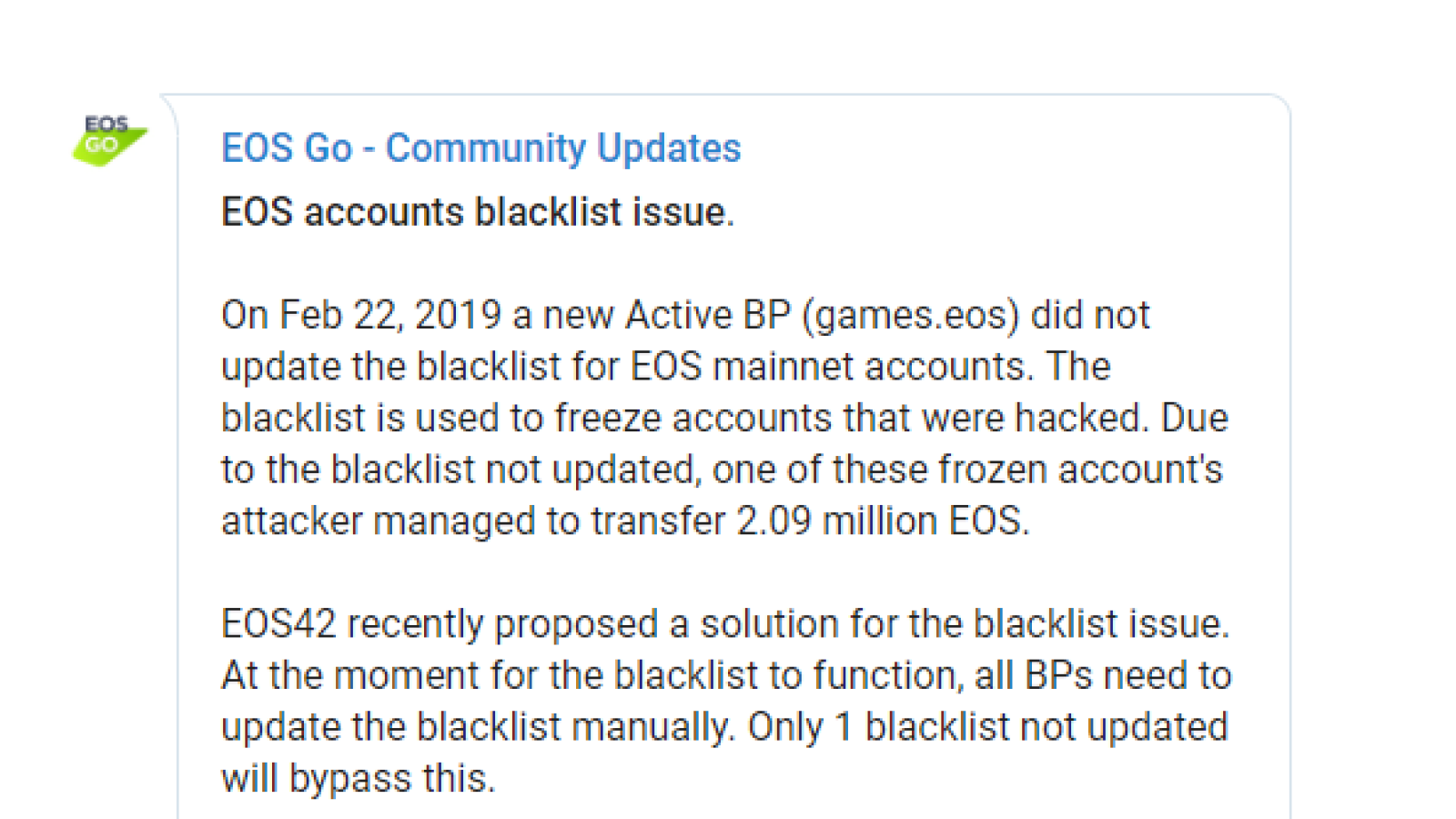
The hack happened the other day, as was reported on the ‘EOS Go’ Telegram channel. The post announced that a hacker succeeded in stealing 2.09 mln EOS tokens from a blacklisted account. This is around $7.7 mln. This became possible due to a new BP failing to update the list of frozen hacked accounts.
Details of the attack
The malicious attack took place after the team behind EOS came up with a way to solve the problem of the broken blacklist and made a public proposal. The EOSIO chain enables Block Producers (BP) to put certain accounts on a blacklist.
Most likely, the cause for the hack is a new BP on the network under the nickname ‘games.eos’ that for some reason failed to upload a new version of the blacklist for the EOS mainnet accounts, thus enabling the culprit to do his dirty job.
The proposal says that EOS BPs have to put an account on a blacklist in order for this list to work appropriately. The ‘loophole’ in the blacklist provides a BP with a veto power to interfere with the 15/21 DPOS consensus.
Should a BP forget or simply avoid updating the blacklist on its node, this BP would be neglecting the decision made by 15/21. This may allow any hacker to take advantage of the accounts blacklisted by the other BPs and transfer crypto from them.
Hacker-hunting underway, accounts frozen
As soon as the hack occurred, the security team of the Huobi exchange checked the data from the blacklist provided by the EOS Core Arbitration Forum (ECAF) in order to spot any crypto flowing out of the EOS accounts put on the blacklist into Huobi wallets.
As a result, the exchange blocked all accounts on its platform that were linked to that blacklist.
A new security solution
The proposal from EOS also suggests eliminating keys for the accounts on the blacklist instead of allowing a BP to place a veto within the mainnet. The new solution will allow returning an account to its initial owner. This seems much easier than working with the blacklist.